The Internet of Things can be used to create a lot of opportunity for your organization, but there are considerable risks that your business can’t forget about, no matter how tempting it is to take advantage of them. Even though security remains a prime concern for businesses, it’s clear that the Internet of Things isn’t going anywhere. Therefore, you might as well embrace it, or at least prepare for it.
opX Blog
If you think about it, password security is an interesting phenomenon. The odds are that a user knows the importance of using a strong password, as well as the potential consequences of using weak ones. Yet, time after time, people would rather go with passwords that are easy to type and remember, as opposed to adding a few simple security measures.
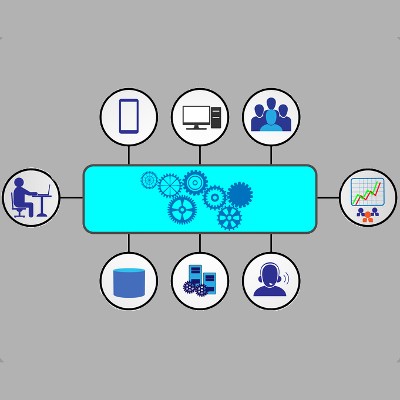
Having quality IT support is essential to keep your business running, but how can you know for sure that you’ve found the support that’s right for your organization? Often times, good IT support can be tricky to find, especially in areas where the technical skills required to perform IT maintenance are sparse. How can you get the support you need without making a difficult compromise?
If you’re looking for an outsourced IT provider, perhaps the best thing you can ask a prospective company is how they can save you money and improve the flexibility of your budget. Break-fix IT can place an unneeded burden on your organization, but managed IT allows you to save money and improve operations all at the same time.
When you decided to start a business, did you ever think that there were so many angles to cover? From the core work that goes on to all the small seemingly mundane details that you have to acknowledge, there is so much work that, for the small business owner, it can be extraordinarily difficult to cover all the bases. This is doubly true when it comes to your company’s technology. If you don’t have the technical expertise to manage your company’s technology, and you don’t have the financial resources to hire a dedicated IT administrator, then you need another option.
Security is a critical component for businesses, regardless of their size. However, since so many considerations need attention, it can be easy to get lost in a swirl of solutions. In times like these, it’s best to get back to basics and make sure you have the essentials covered. To help, here are two steps to help you evaluate your initial security implementation and current processes.
There’s no denying that education, whether through a professional or autodidactic medium, is important in cybersecurity. While it’s not always the case, organizations like to hire people with a formal education. The problem in this case is that most educational institutions do little to foster an understanding of actual cybersecurity.
Your phone is a repository of data that hackers would be glad to get their hands on. This is especially true of company devices. For the sake of your business, you need to keep your mobile data safe. Therefore, for this week’s tip, we’re going to show you how to connect your Android device to a VPN.
Many businesses may be holding themselves back by not committing to the proper use and maintenance of their technology. As a result, worker productivity suffers and consequently, so does the business’s return on their tech investments. Is your technology holding your business back from maxing out profits?
So you’re in the market for an IT provider. What is it that you look for? Do you want a provider who waits until your technology is broken before taking action, or would you prefer one who prevents this from happening in the first place? Chances are that you’re of the former mindset, and you’re not alone. More businesses than ever are switching from break-fix IT to managed IT services.
We often think of encryption in terms of the computing sense of the word. Data is scrambled to prevent it from being stolen and used for nefarious purposes. However, encryption has been around for quite some time, dating back to ancient times. At its heart, encryption (a type of cryptography) must be defined as the protection of secrets.
The Internet has long been a great tool for business, but you can’t take advantage of it without putting your sensitive data at risk of threats, like hackers and malware. Granted, when it comes to cyber security, even the most cautious business will have a lot on their plate. We’ll go over eight of the most important security best practices, and how you can implement them for your business.
opX is proud to announce the launch of our new website at http://www.opxllc.com/. The goal of the new website is to make it easier for our existing clients to submit and manage support requests, and provide more information about our services for prospective clients.
 When you mention the term 'disaster recovery,' most people think about the big ground-shattering events like earthquakes, fires, floods, tropical storms, etc. While these natural events are certainly disasters and devastating in their own right, smaller things can constitute as a disaster for your business, and they aren't seasonal.
When you mention the term 'disaster recovery,' most people think about the big ground-shattering events like earthquakes, fires, floods, tropical storms, etc. While these natural events are certainly disasters and devastating in their own right, smaller things can constitute as a disaster for your business, and they aren't seasonal.
 Email is (and has been) a prime method of communication for businesses of all sizes. With email comes a whole slew of issues that are essentially synonymous with the technology; spam, information overload, phishing, and information privacy. Even Nationwide small businesses that only do business locally are at risk of these issues. Personal email accounts are equally at risk. Employing proper precautions and practices whenever communicating via email is very important to prevent the risk of security compromises, monetary loss, and even legality issues.
Email is (and has been) a prime method of communication for businesses of all sizes. With email comes a whole slew of issues that are essentially synonymous with the technology; spam, information overload, phishing, and information privacy. Even Nationwide small businesses that only do business locally are at risk of these issues. Personal email accounts are equally at risk. Employing proper precautions and practices whenever communicating via email is very important to prevent the risk of security compromises, monetary loss, and even legality issues.